CAPTCHA AI Powered by Large Models: Why It's More Suitable for Enterprise Scenarios
Ethan Collins
Pattern Recognition Specialist
CAPTCHA technology is being redefined by AI visual recognition capabilities. Many still view CAPTCHA as a simple "component," but in real-world automated processing environments, it has evolved into a continuous advancement between AI visual technology and verification mechanisms.
I. CAPTCHA Evolution: From OCR to AI Visual Recognition
1. First Generation: The OCR Era (2000-2010)
Technical Background
The core problems faced by the early internet were spam and automated program abuse. reCAPTCHA emerged as a pioneering system, with a simple design philosophy: leverage human advantages in visual recognition to create barriers difficult for machines to overcome.
Typical Implementations
- Distorted English character strings (4-6 digits)
- Added interference lines, noise, background textures
- Color contrast interference
Evolution of Automated Recognition Technology
| Phase | Technical Method | Recognition Efficiency |
|---|---|---|
| 2003-2005 | Traditional OCR (Tesseract) + Rule Correction | 30-50% |
| 2005-2008 | Image Preprocessing (denoising, binarization, segmentation) + SVM | 60-80% |
| 2008-2010 | Convolutional Neural Networks (LeNet-5 improved version) | 90%+ |
Milestone Event
In 2008, research published in Science demonstrated that machine recognition rates for text-based CAPTCHAs were rapidly improving. This directly spurred the birth of the second generation of CAPTCHAs.
Core Insight: Fixed character sets + limited distortion rules = collectible datasets = easily recognized by automated systems.
2. Second Generation: Behavioral + Image Challenges (2010-2020)
Paradigm Shift
CAPTCHA designers realized that simply increasing recognition difficulty would also negatively impact real user experience. It became necessary to introduce "human-exclusive capabilities"—semantic understanding and behavioral patterns.
Analysis of Three Major Commercial Systems
reCAPTCHA (Google)
- v2 (2014): "I'm not a robot" checkbox + invisible risk analysis
- Core Technology: Risk Analysis Engine, based on 100+ signals (Cookie, device history, subtle mouse movements, page interaction timing)
- Image Challenges: Real-world scenes extracted from Street View (traffic lights, crosswalks, buses), using crowdsourced labeling to simultaneously train autonomous driving models
GCaptcha (Intuition Machines)
- Differentiated Positioning: Privacy-first, claims not to track user personal data
- Technical Features: Distributed verification architecture, challenge images from client's own datasets, forming a "verification as labeling" business model
- Verification Design: Dynamic difficulty adjustment, real-time switching of challenge types based on automated processing pressure
GeeTest
- Core Innovation: Slider verification + jigsaw puzzle restoration, transforming "recognition" into "operation"
- Behavioral Data Collection: Trajectory coordinate sequences (typically 50-200 points), velocity curves, acceleration changes, touch events (mobile)
- Risk Control Dimensions: Not only determines pass/fail, but also outputs a "human confidence score" for business-level decision-making
Development of Automated Processing Technology
| Automation Type | Technical Method | Verifier's Response |
|---|---|---|
| Automated Image Recognition | Object Detection (YOLO/Faster R-CNN) + Semantic Segmentation | Dynamic image generation, adversarial samples |
| Slider Trajectory Simulation | Physics engine simulation (Bezier curves, noise injection) | Time-series analysis, biometric recognition |
| Crowdsourced Platform Processing | Crowdsourcing platforms (cost $0.5-2/thousand) | Rate limiting, correlation analysis, reputation systems |
| Browser Automation | Selenium, Puppeteer, Playwright | Browser fingerprint detection, automated feature recognition |
Core Challenges
The core assumption of second-generation systems was that automated programs could not simulate human behavior at scale. However, with the development of deep learning, this assumption is being challenged:
- Trajectory Generation: GANs can learn the dynamic characteristics of real user mouse movements
- Image Understanding: Breakthroughs in Vision Transformers (ViT) on ImageNet have brought machine vision close to human levels.
- Browser Fingerprinting: Randomization techniques for automated framework fingerprints are becoming increasingly sophisticated
Core Insight: Any fixed challenge, no matter how cleverly designed, is essentially an "exam with standard answers." As long as there are standard answers, they can be collected, learned, and ultimately processed by automated programs.
II. Development and Challenges of AI Visual Recognition Technology
1. Industrialized System for Automated Recognition
Modern CAPTCHA automated recognition has formed a complete industrialized system with highly specialized technology stacks:
Data Layer
- Collection Systems: Distributed crawler clusters, 24/7 fetching challenges from target sites
- Labeling Factories: Low-cost data labeling teams, or semi-automated labeling tools (SAM-assisted)
- Data Augmentation: Rotation, cropping, color transformation, adversarial noise to expand training set diversity
Model Layer
| Task Type | Model Architecture | Open-source Implementation Reference |
|---|---|---|
| Character Recognition | CRNN + CTC | PaddleOCR, EasyOCR |
| Object Detection | YOLOv8, RT-DETR | Ultralytics |
| Image Classification | ViT, ConvNeXt | Hugging Face Transformers |
| Slider Trajectory | Seq2Seq, Diffusion Model | Community open-source solutions |
| Multimodal Understanding | CLIP, LLaVA | OpenAI CLIP, Alibaba Qwen-VL |
Engineering Layer
- Inference Optimization: TensorRT, ONNX Runtime, OpenVINO for millisecond-level response
- Service Architecture: Kubernetes orchestration, auto-scaling, supporting high-concurrency requests
- Automated Bypass: Browser fingerprint randomization, IP proxy pools, behavioral rhythm simulation
Analysis of the OpenClaw Phenomenon
The recent highly popular OpenClaw project represents the trend of "democratization of AI visual recognition tools":
- Low Barrier: Pre-trained models + configuration files can target specific objectives
- Modularity: Decoupling of data collection, model training, inference services, and result submission
- Community-Driven: Sharing of recognition samples, model weights, and iterative technical solutions
Impact on Enterprises: What previously required specialized security teams to implement automated recognition can now be quickly adopted by ordinary developers. This significantly raises the technical requirements for CAPTCHA verification mechanisms.
2. Verification Mechanisms: From "Static Challenges" to "Dynamic Risk Control"
Paradigm Shift: Rise of Behavioral Modeling
The core transformation of enterprise-grade CAPTCHA systems is from "verifying answer correctness" to "assessing behavioral authenticity." This is analogous to the evolution of financial risk control from "rule engines" to "machine learning scorecards."
Multi-dimensional Behavioral Fingerprint System
| Data Collection Dimension | Technical Indicators | AI Analysis Method |
|---|---|---|
| Mouse Dynamics | Trajectory point density, velocity curves, acceleration distribution, angle changes | LSTM/Transformer time-series modeling, comparison with real user baseline distribution |
| Keyboard Interaction | Key press intervals (Keydown-Keyup), key combination patterns, correction behaviors (Backspace frequency) | Rhythm analysis, detection of uniform interval characteristics of automated tools |
| Touch Events (Mobile) | Pressure value, contact area, sliding inertia, multi-touch patterns | Biometric recognition, distinguishing human fingers from robotic arms/simulators |
| Visual Attention | Eye tracking (if permitted), page scrolling patterns, element focus timing | Attention heatmap analysis, detection of non-human browsing patterns |
| Cognitive Reaction Time | Delay from challenge presentation to first interaction, decision time distribution | Statistical testing, automated tools are often too fast or too slow |
| Environmental Context | Device posture (gyroscope), battery status, network latency fluctuations | Anomaly detection, identification of virtual machines/simulators/cloud phones |
Key Role of Large Models
Traditional rule engines struggle to handle high-dimensional, non-linear behavioral sequences. Large models (especially Transformer architecture) bring breakthroughs:
- Representation Learning: Encoding raw behavioral sequences into low-dimensional embeddings to capture deep patterns
- Transfer Learning: Pre-training with massive unsupervised behavioral data, fine-tuning with small samples to adapt to new scenarios
- Multimodal Fusion: Unified processing of image, time-series, and categorical features for end-to-end optimization
III. Why Large Model CAPTCHA Visual Recognition is More Suitable for Enterprise Scenarios
Data Flywheel: In the Era of Data Dominance, Enterprises' Unique Competitive Advantage
Comparison of Automated Recognizer vs. Verifier Data
| Data Type | Available to Automated Recognizer | Actually Owned by Enterprise Verifier | Strategic Value |
|---|---|---|---|
| Successful Recognition Cases | ✅ Limited samples (requires costly collection) | ✅ Massive failed cases (automated recognition logs) | Training "automated pattern recognition" models |
| Real User Behavior | ❌ Difficult to obtain at scale | ✅ Full business traffic | Building "human behavior baselines" |
| Automated Tool Fingerprints | ❌ Passively discovered | ✅ Proactive detection + honeypot collection | Identifying automated framework characteristics |
| Time-series Correlated Data | ❌ Single-point perspective | ✅ Global view across business lines | Correlation analysis, identifying organized automated behavior |
Continuous Learning Loop
[Production Traffic] → [Behavioral Data Collection] → [Feature Engineering] → [Model Inference] → [Risk Scoring]
↑ ↓
[Model Update] ← [Performance Evaluation] ← [Labeling Feedback] ← [Business Decision]
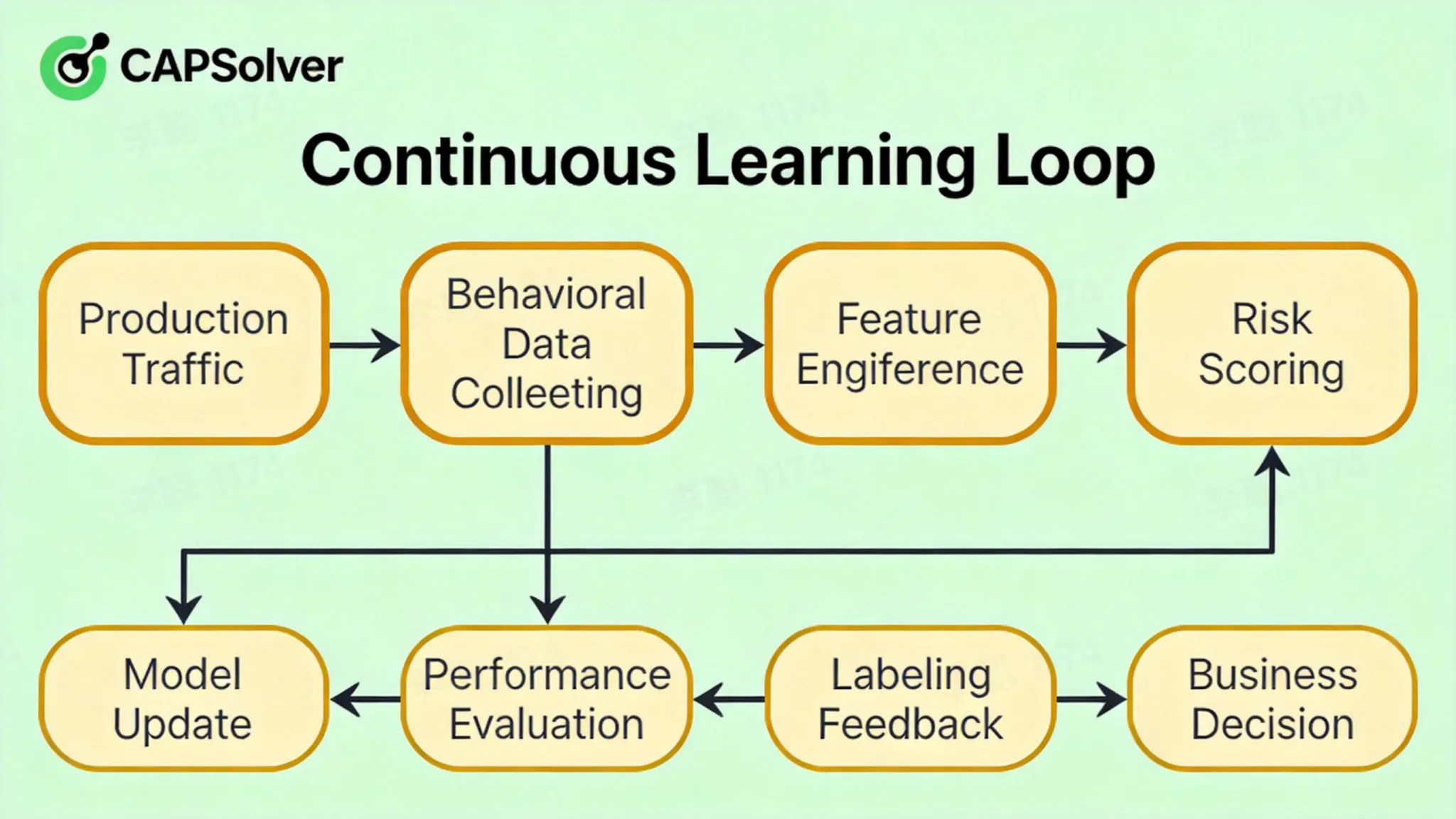
- Online Learning: Model parameters are fine-tuned in real-time with new data, without requiring full retraining
- Active Learning: Intelligently selecting high-value samples for manual labeling, optimizing labeling ROI
- Adversarial Training: Enhancing robustness by using automated recognition samples as negative examples
Deep Integration with Business Risk Control
| Integration Scenario | Technical Implementation | Business Value |
|---|---|---|
| Login Protection | CAPTCHA score + device fingerprint + IP reputation → unified risk score | Precisely intercept automated logins, reduce false positives |
| Registration Anti-fraud | Abnormal verification behavior → trigger phone/email secondary verification | Identify batch registrations, protect user pool quality |
| Marketing Activities | Flash sales scenarios, real-time human-machine recognition → dynamic rate limiting | Prevent automated snatching, protect real user rights |
| Payment Security | Mandatory verification before high-risk operations + behavioral review | Block automated fraudulent transactions, reduce asset loss |
For more insights on modern automation, see our guide on why web automation keeps failing on CAPTCHA
IV. Private Deployment Evolution Path
Typical Journey from Experiment to Production
Phase One: Proof of Concept (PoC, 1-2 months)
- Scenario: Security team assesses the vulnerabilities of existing CAPTCHAs, or business complains about poor verification experience
- Action: Simulate automated recognition using tools like OpenClaw, quantify recognition cost and success rate
- Output: Automated recognition feasibility report, preliminary ROI estimation
Phase Two: Pilot Deployment (Pilot, 3-6 months)
- Technology Stack: Open-source models (YOLO + ResNet) + self-built labeling team
- Core Challenges:
- Poor model generalization, rapid failure when new automation types appear
- High inference latency, impacting user experience
- Lack of behavioral analysis dimensions, relying solely on image recognition
- Key Decision: Whether to invest resources in building an MLOps platform or purchasing a commercial solution
Phase Three: Production at Scale (Production, 6-12 months)
- Architecture Upgrade:
- Inference Layer: Triton Inference Server + TensorRT, GPU utilization optimization
- Data Layer: Real-time feature store (Redis/Flink) + offline data lake (Iceberg/Delta Lake)
- Training Layer: Kubeflow/MLflow for managing experiments and model versions
- Organizational Development: Establish a dedicated AI security team (algorithm engineers + backend engineers + security analysts)
Phase Four: Platform Operation (Platform, 1-2 years)
- Capability Output: CAPTCHA service as an internal security middleware, supporting multiple business lines
- Ecosystem Integration: Linkage with threat intelligence, SOC (Security Operations Center), SIEM systems
- Continuous Verification: Establish red-team/blue-team verification mechanisms, regularly simulate APT-level automated recognition drills
V. Enterprise vs. Non-Enterprise: Comprehensive Comparison
| Comparison Dimension | Non-Enterprise Solutions (OpenClaw / Traditional OCR) | Enterprise CAPTCHA AI Visual Recognition |
|---|---|---|
| Deployment Complexity | ✅ Simple, Docker one-click startup | ❌ Complex, requires MLOps platform support |
| Initial Cost | ✅ Low, single GPU sufficient | ❌ High, requires cluster + labeling team |
| Model Updates | ❌ Fixed weights, easily targeted by automated recognition | ✅ Online learning, continuous evolution |
| Behavioral Analysis | ❌ Pure image recognition, no behavioral dimension | ✅ Multimodal fusion, precise human-machine differentiation |
| Risk Control Linkage | ❌ Isolated system, no contextual awareness | ✅ Deep integration with WAF, device fingerprints |
| High Availability | ❌ Single point of deployment, no SLA guarantee | ✅ Multi-active architecture, elastic scaling |
| Compliance Support | ❌ Weak audit logs, privacy compliance | ✅ GDPR/CCPA adaptation, complete audit |
| Applicable Scenarios | Small and medium businesses, internal testing, short-term projects | Large-scale production, finance, e-commerce, government affairs |
VI. Future Form: AI Risk Control Infrastructure
Technology Evolution Trends
| Evolution Direction | Current State | Next 3-5 Years |
|---|---|---|
| Verification Method | Passive challenges (user required to perform actions) | Invisible CAPTCHA, based on background behavioral analysis |
| Model Architecture | Specialized small models (CNN/LSTM) | Multimodal large models (GPT-4V-like architecture fine-tuning) |
| Challenge Generation | Fixed question bank + limited variations | Generative AI real-time synthesis (one question per person, every question different) |
| Decision Logic | Binary classification (human/machine) | Continuous risk scoring + dynamic strategy orchestration |
| Verification Mode | Single-point verification | Federated learning collaboration, industry-level automated recognition intelligence sharing |
Imagination Space for Generative CAPTCHA
Using Diffusion Models or GANs to generate verification content in real-time:
- Advantages: No pre-stored question bank, automated recognizers cannot collect training data in advance
- Challenges: Control of generation quality (avoiding samples difficult for humans to recognize), optimization of inference costs
- Frontier Research: Industry rumors suggest systems like reCAPTCHA v4 may incorporate generative technology.
VII. Recommendations for Technical Decision-Makers
| Time Dimension | Action Item | Key Milestone | Goal |
|---|---|---|---|
| Short-term (1-3 months) | Automated Recognition Surface Assessment | Complete OpenClaw simulated automated recognition, quantify current CAPTCHA MTBF | Establish risk awareness, secure resource investment |
| Monitoring System Construction | Deploy automated recognition detection rules, identify automated traffic characteristics | From "passive response" to "visible recognition" | |
| Mid-term (3-12 months) | Data Infrastructure | Build behavioral data collection pipelines, accumulate 10 million+ labeled samples | Possess the data foundation for training production-grade models |
| Model Iteration and Launch | First deep learning model A/B testing, verify recognition defense effectiveness | Prove technical feasibility, build team confidence | |
| Long-term (1-2 years) | Platformization | CAPTCHA service SLA reaches 99.99%, supports 100,000 QPS | Become a core security infrastructure for the company |
| AI Security Strategy | Integrate into a unified risk control platform, link with anti-fraud | Form a multi-dimensional AI verification system |
VIII. CapSolver's AI Visual Recognition Capabilities
As a technology provider focused on delivering efficient and stable AI visual recognition services, CapSolver possesses significant advantages in image CAPTCHA recognition and custom solver training:
- Supports various image-based CAPTCHAs: CapSolver has deeply optimized its recognition algorithms for mainstream and complex image CAPTCHAs, supporting types including but not limited to image classification and object detection.
- Rapid adaptation to new CAPTCHAs: Based on advanced large visual model technology, CapSolver can achieve few-shot learning and rapid fine-tuning, helping enterprises quickly adapt to new CAPTCHA challenges appearing in the market.
- Enterprise-grade API and high-concurrency processing capabilities: CapSolver provides stable, highly available enterprise-grade API interfaces that support high-concurrency requests, ensuring millisecond-level responses to meet enterprises' needs for large-scale automated data collection.
- Custom Solver Training: For enterprises' specific visual recognition needs, CapSolver offers customized model training services, helping enterprises build exclusive, high-precision CAPTCHA recognition solutions.
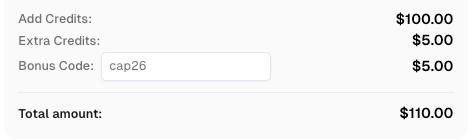
Use code
CAP26when signing up at CapSolver to receive bonus credits!
IX. Further Reading and Industry References
| Resource Type | Recommended Content | Value |
|---|---|---|
| Open Source Projects | OpenClaw & CapSolver | Understanding automated recognition technology stacks |
| Industry Reports | Gartner Market Guide for Fraud Detection | Reference for commercial solution selection |
X. Conclusion
With the rapid advancement of AI technology, CAPTCHA recognition is no longer a simple technical challenge but a critical capability for enterprises to acquire public data and ensure business continuity in the digital age. AI visual large models, with their excellent complex scene understanding, powerful generalization capabilities, and efficient model scalability, provide unprecedented solutions for enterprise-level automated recognition. CapSolver, with its deep accumulation in AI visual recognition and enterprise-grade service capabilities, is committed to being your trusted partner, helping enterprises efficiently and compliantly address various CAPTCHA challenges, and focus on creating core business value.
XI. Frequently Asked Questions (FAQ)
Q1: How do Large Visual Models (LVMs) differ from traditional CNNs in CAPTCHA recognition?
A1: Unlike traditional CNNs that rely on local feature extraction, LVMs utilize architectures like Vision Transformers (ViT) to capture global context and semantic meaning. This allows them to understand complex scenes and generalize to new, unseen CAPTCHA styles with much higher accuracy and minimal additional training.
Q2: What is "Few-shot Learning" in the context of AI-based CAPTCHA solvers?
A2: Few-shot learning refers to the ability of a pre-trained AI model to adapt to a new task (like a new type of CAPTCHA) using only a very small number of labeled examples. This is a core advantage of large models, enabling rapid deployment against evolving verification mechanisms.
Q3: What types of image CAPTCHAs does CapSolver support?
A3: CapSolver has deeply optimized its recognition algorithms for mainstream and complex image CAPTCHAs, supporting types including but not limited to image classification and object detection.
Check the image Solution : Imagetotext & VisionEngine
Q4: How does CapSolver ensure the accuracy and stability of recognition?
A4: CapSolver is based on advanced large visual model technology, continuously optimizing model performance through a continuous learning loop and online learning mechanisms. Additionally, we provide enterprise-grade APIs and a high-concurrency architecture, ensuring millisecond-level responses and 99.9% availability.
Q5: Does CapSolver's service support private deployment?
A5: CapSolver offers flexible deployment options, including cloud services and private deployment, to meet the security and compliance needs of different enterprises. Private deployment solutions can be customized based on the enterprise's specific architecture and resources.
More
AIApr 28, 2026
AI Agents in Web Scraping & Competitive Intelligence Guide
Discover how AI agents transform web scraping and competitive intelligence. Learn about automated data collection, anti-bot challenges, and CAPTCHA solutions for scalable workflows.
AIApr 24, 2026
AI Agent vs Chatbot: Key Differences in Automation Capabilities
Discover the key differences between AI agent vs chatbot. Learn how agentic AI outperforms traditional AI in automation, decision-making, and complex workflows.